LFI On the Documentation Page

I know it’s been a very long time since I last published my article on how I was able to find RCE on Bentley systems. For the last 1–1.5 years, I was doing internships in various companies and that’s why I don’t have time for doing bug bounties. After some months of internship, my mind said to me that

So I left the internship and got back to hitting bounties.
The Finding:-
I had accepted a lot of private invites on Bugcrowd. But never started hunting on them. In the mid of February, thought to try on a random private target that I had accepted.
I’m not in the recon process very much, so I just casually started surfing the website while running burp in the background but nothing special came up.
As there are already 81 bugs reported, So I thought that let’s try to hunt on very underrated endpoints like:-
- Careers Page
- KnowledgeBase/Docs Page
- Contact Us
Finally, somehow I had managed to find a self XSS on the contact-us page and chained it with CSRF to make it exploitable and then reported it. But I wanted to find a P1 that’s my goal. So secondly, I went on the resources page and saw that there was EBOOK central(books about how to use the company’s product) and a download book feature also.

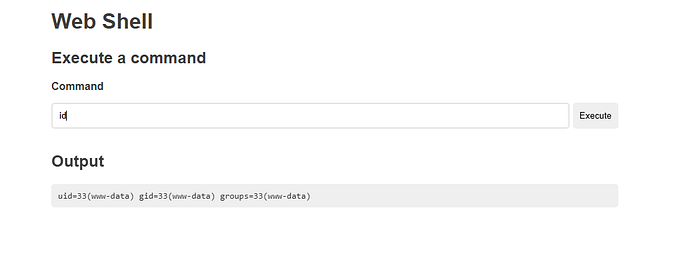
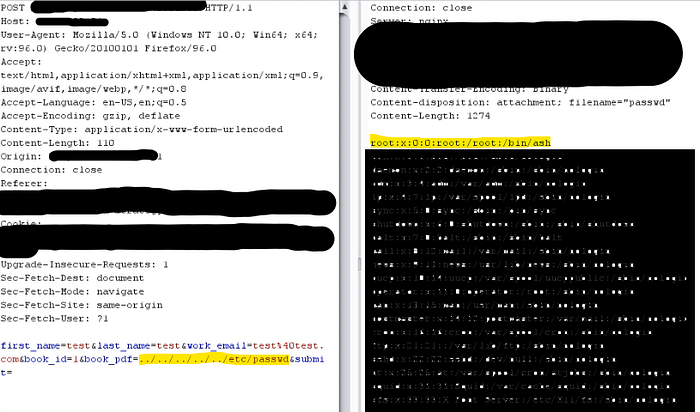
After filling in all the required information I captured this request in BURP SUITE and the request was look like as below:

And in the above request, the vulnerable parameter was book_pdf. So I had first set the value of book_pdf to ../../../../etc/passwd, but sadly it returns 403 forbidden.
At this stage, I tried all possible ways to bypass the WAF(CloudFront) but nothing worked for me, then I remember what if we find the ORIGIN IP behind the CloudFront. We can bypass the WAF.
After some censys Dorking, I was able to find the actual ORIGIN IP and the result is below:
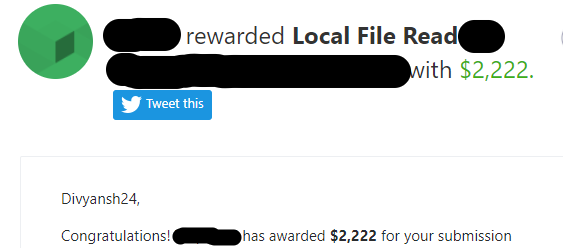
then Reported to the Company and they rewarded me with $2222.
If you need assistance in securing your company, please feel free to send me a direct message. I’m here to help.
Feel free to reach out:
EMAIL: divyanshsharma2401@gmail.com
LINKEDIN: https://www.linkedin.com/in/divyanshsharma24/
TWITTER: https://twitter.com/divyansh2401
Thanks for reading my write-up.